Blog

Blog
March 2026
GetReal's head of threat research attended the 2026 Deepfake Summit in Houston and returned with sharp observations: synthetic identities are already inside your institution, eKYC is losing the battle, and the rise of AI agents is about to make proving you're a real human far more critical.




Blog
February 2026
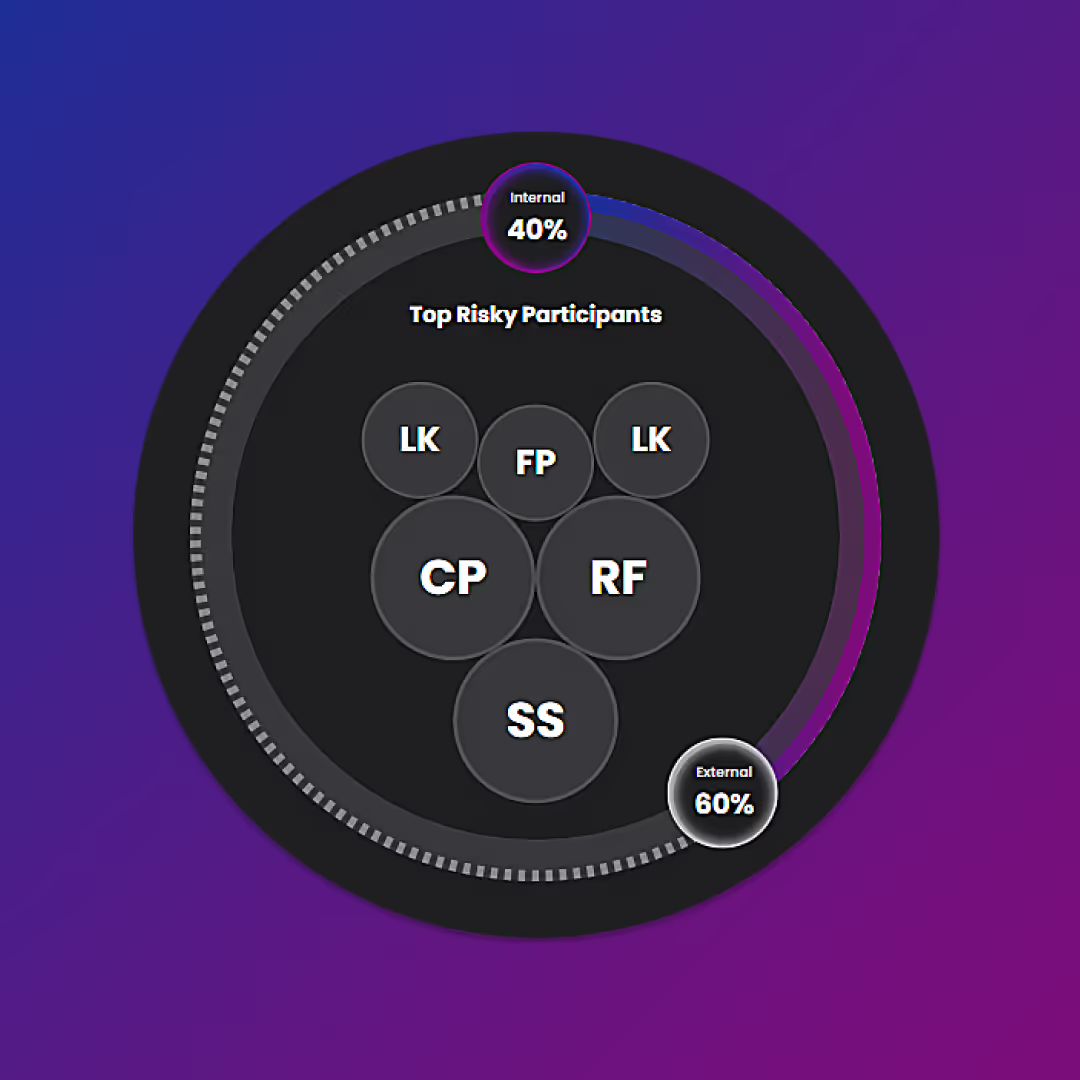
In the past, IT service help desks have counted on multi-factor authentication (MFA), biometrics, caller ID, training, scripts, escalation, and policies to prevent social engineering. But when employee and customer identity can be impersonated at scale, those approaches are no longer sufficient.




Blog
January 2026
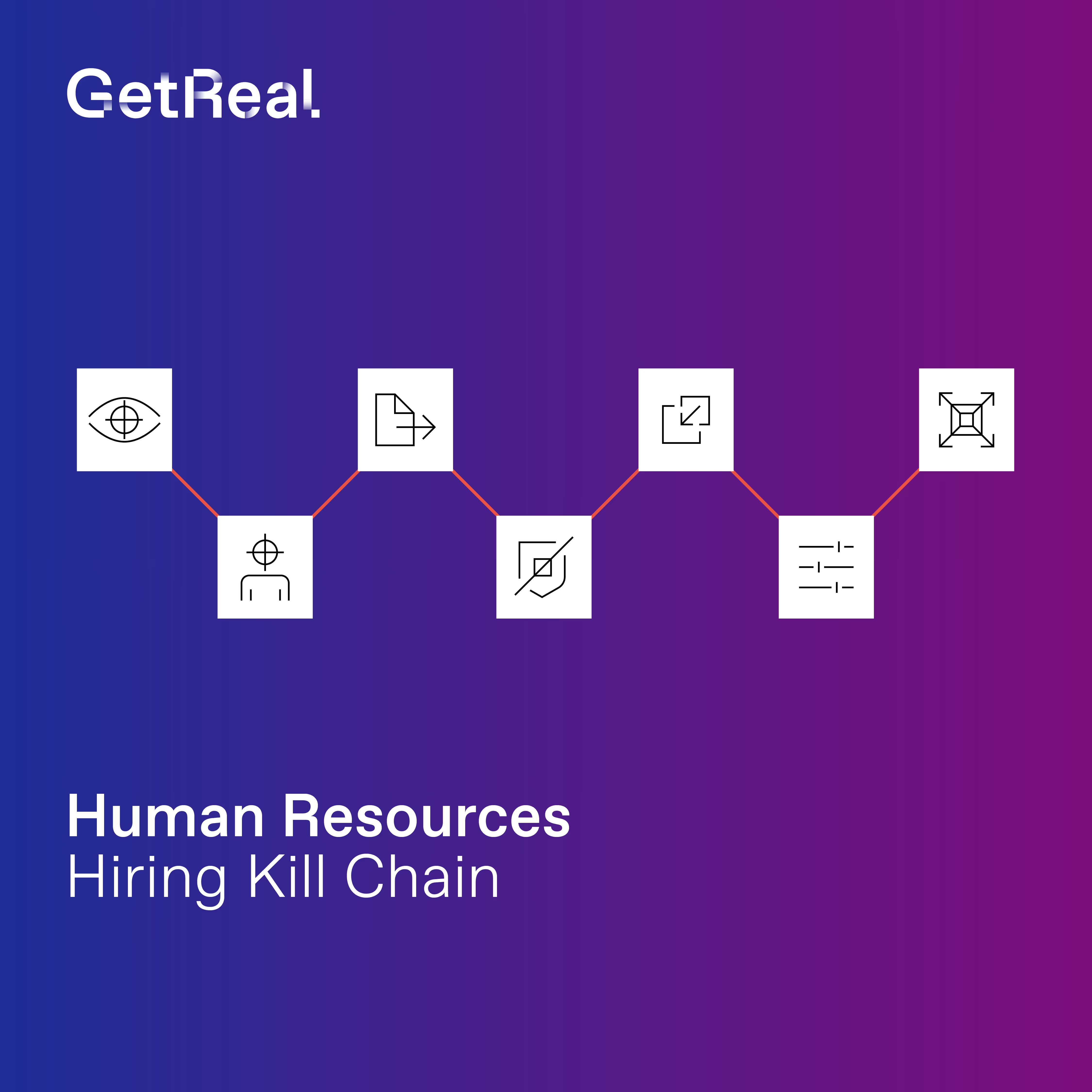
North Korea’s remote IT worker operations are not slowing down—they’re succeeding. This post explains why traditional hiring and background checks fail against highly organized DPRK campaigns, and why organizations must rethink hiring through a zero-trust, human capital supply chain lens.