AI Weaponizes Trust Across Your Business Operations

The Stakes in the Enterprise
Source: Surfshark
.avif)
Source: Ponemon Institute
Source: Gartner
Why the Human Layer is an Enterprise Access Point
Enterprises today operate through a fabric of digital interactions people tend to trust implicitly: executive video calls, HR interviews, IT help desk escalations, vendor onboarding, and finance approvals.
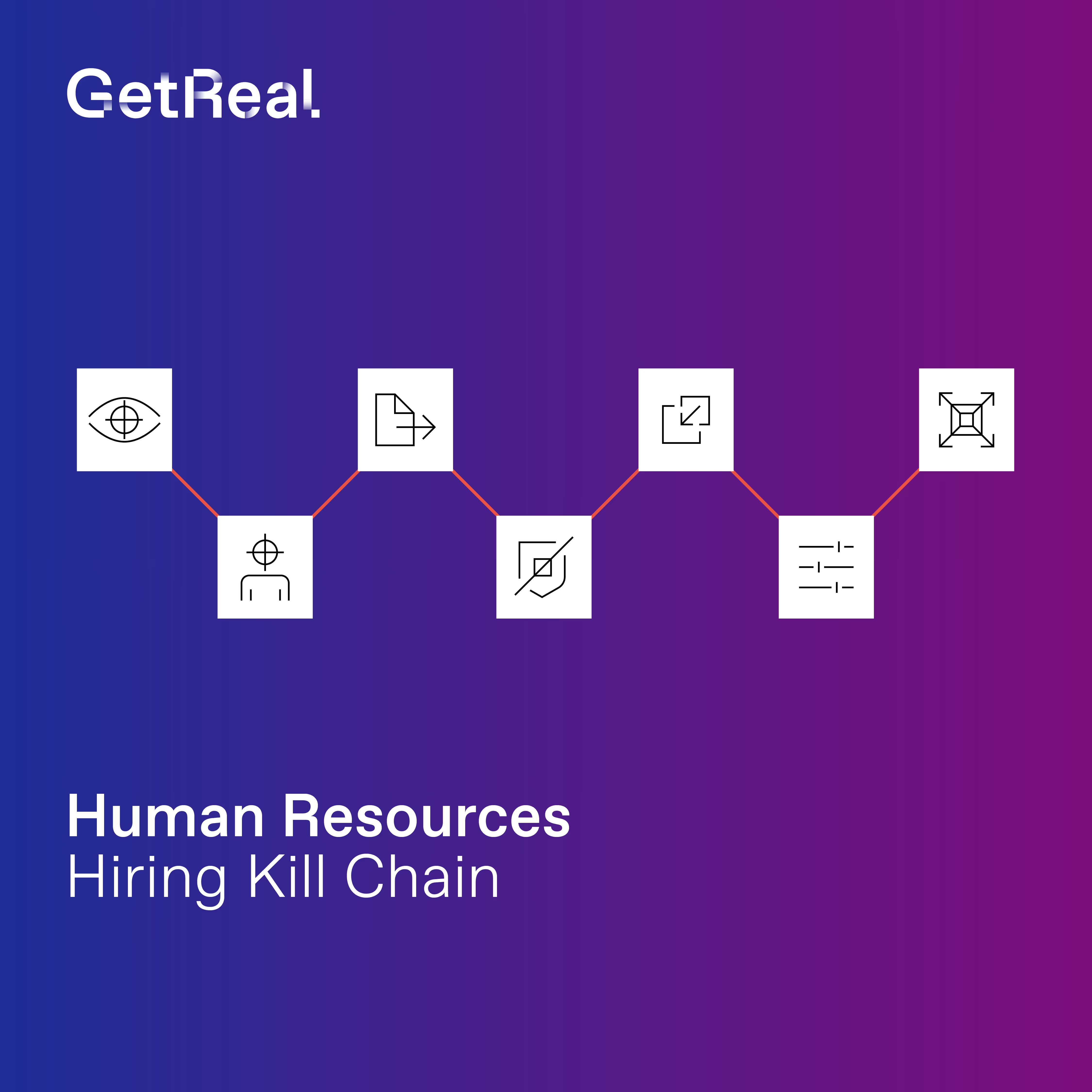
That implicit trust is now the attack surface. Nation-state operatives use AI-synthesized personas to infiltrate hiring pipelines. Scattered Spider-style actors impersonate IT staff for account takeover. Criminals deploy executive deepfakes to authorize fraudulent wire transfers.
Enterprises’ most consequential workflows share a common vulnerability and existing security controls are blind to it.
What’s at Risk
- Financial loss from wire transfer and payment fraud when deepfake-impersonated executives or vendors authorize transactions that bypass existing approval controls
- Nation-state and insider threat exposure when adversaries use synthetic identities to gain employment, embed in corporate systems, and exfiltrate data or establish backdoor access over time
- IT and account takeover risk when help desk staff are socially engineered via cloned customer voices or impersonated employee identities to reset credentials or grant privileged access
- Legal, regulatory, and audit liability when identity-based fraud occurs in workflows your controls were expected to govern and you lack the forensic evidence to demonstrate due diligence
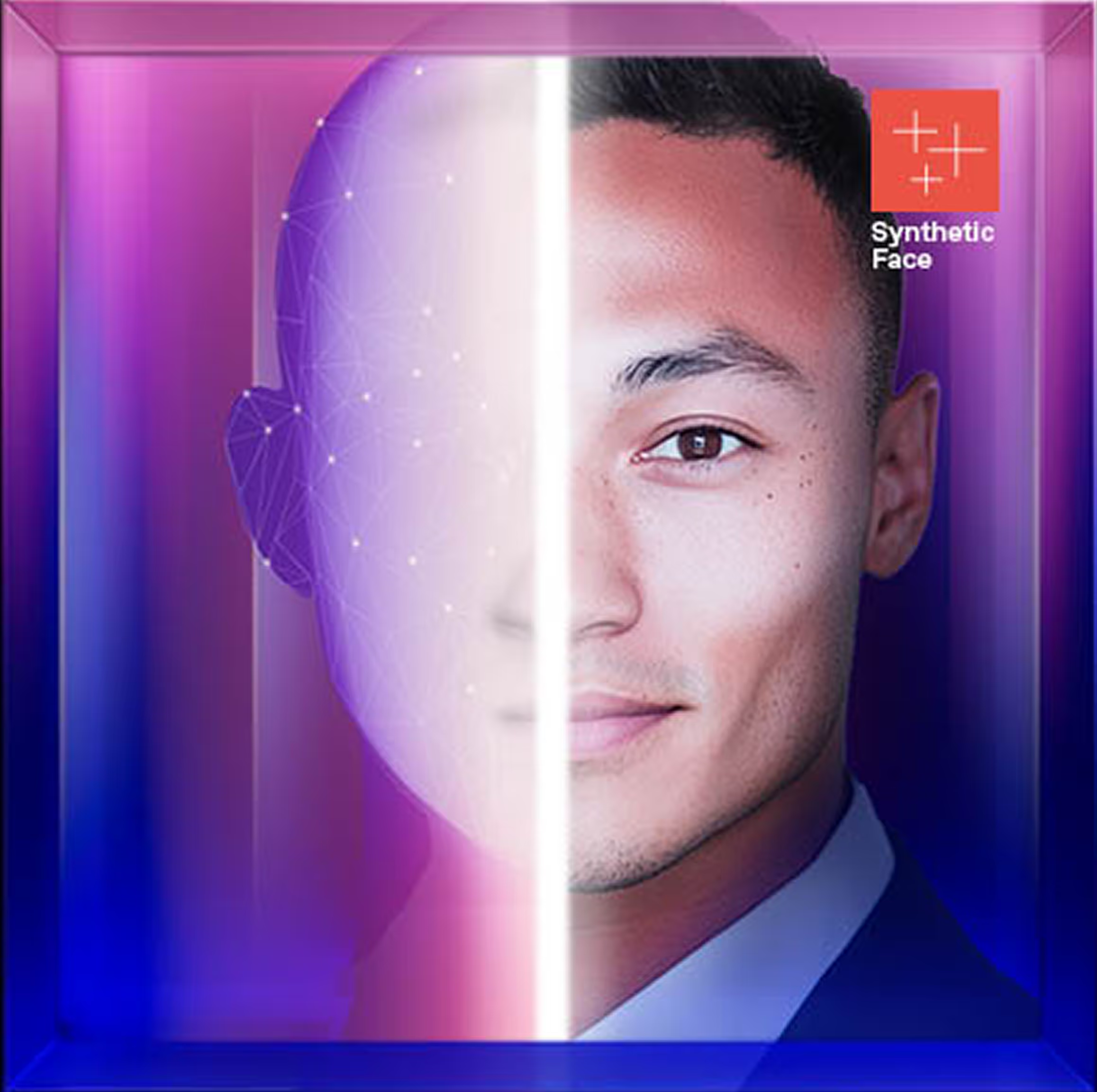
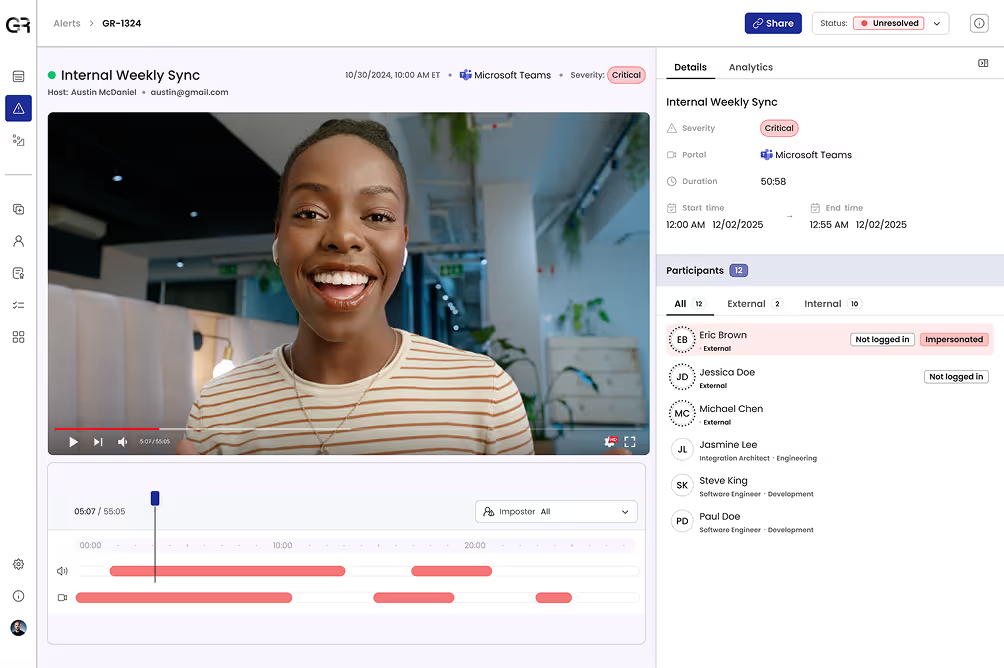
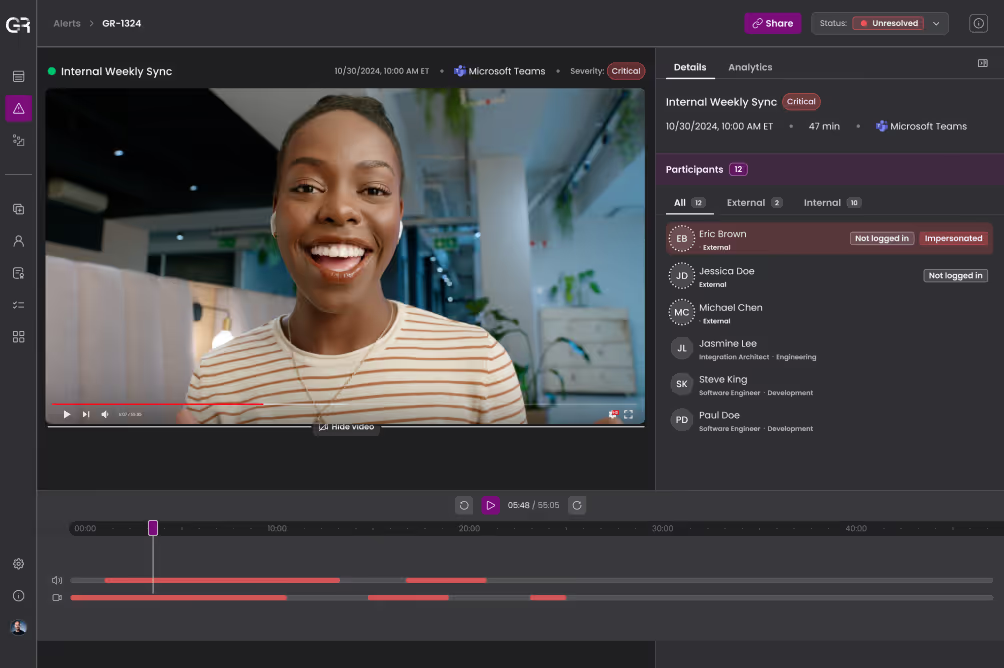
Rigorous Deepfake Detection
GetReal applies forensic-science-based media analysis to detect manipulation in real-time voice and video calls, recorded meetings, executive communications, and candidate interviews. Detections are explainable and evidence-backed, giving your security and fraud teams findings they can act on and defend.
Continuous Identity Verification
GetReal builds deep knowledge of identities over time, continuously confirming via face, voice and more that the person appearing in a digital interaction is who your enterprise verified them to be. This creates an asymmetric advantage through accumulated authenticity signals adversaries can’t replicate.
Adaptive, Automated Response
When a threat is identified, GetReal automatically triggers responses across existing security, HR, communications, and IT platforms without a human needing to intervene. Security leaders get the forensic backend data to support every decision, with the defensible audit trail required if an incident is ever investigated, litigated, or reviewed by regulators.
Global Threat Intelligence
Flag repeat offenders and known fraudsters before they enter your pipeline with curated threat intelligence including known fraudulent personas, fake staffing agencies, and North Korea-linked networks.
Why Enterprises Choose GetReal
GetReal delivers unified defense against the AI-powered identity attacks that no single team's existing tools were built to address.
The platform integrates seamlessly into the workflows that matter most — hiring, IT, finance, executive communications — operating invisibly in the background without adding friction for employees or customers. When a threat is identified, response is automatic.
When an incident occurs or an auditor asks, GetReal provides the forensic evidence to support every decision and demonstrate that reasonable controls were in place.
Find Your GetReal Use Case
Understand Deepfake & AI-Powered Identity Threats by Role
Your Enterprise Perimeter May Be Protected. Your Human Layer is Not.