AI-Powered Identity Attacks are Targeting Your People and Your Supply Chain

The Stakes in Defense Contracting
Source: CybelAngel
.avif)
Source: 2025 Verizon DBIR
Source: CrowdStrike
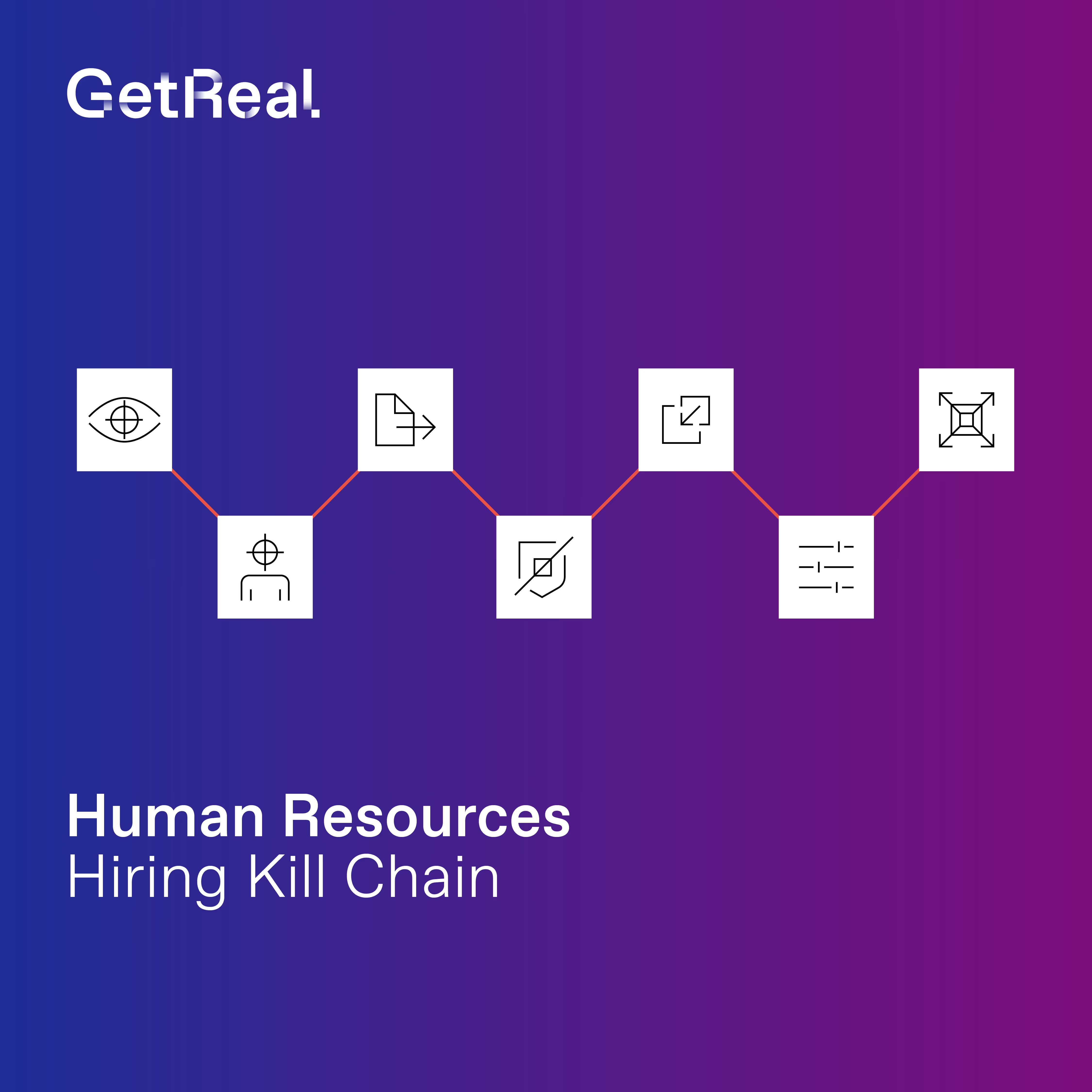
How Defense Contractors are Being Infiltrated
AI, deepfakes, and remote hiring and work have changed what it takes to infiltrate the defense industrial base.
Nation-state operatives no longer need physical proximity, but only a convincing synthetic persona. Google’s Threat Intelligence Group has documented China, Iran, and North Korea all directly targeting defense contractor personnel through hiring processes, spoofed recruitment portals, and other social engineering.
Once inside they access classified programs, exfiltrate data, and establish persistent access across supply chain networks. In 2024, a North Korean IT worker exfiltrated International Traffic in Arms Regulations (ITAR)-controlled data from a California defense contractor.
What’s at Risk
- Program integrity and classified data exposure when nation-state operatives gain insider access through hiring pipelines or impersonation of personnel
- Supply chain compromise when adversaries impersonate vendors or subcontractors in calls seeking to redirect funds, steal credentials, or exfiltrate Federal Contract Information (FCI), Controlled Unclassified Information (CUI), and more
- Cybersecurity Maturity Model Certification (CMMC) and Defense Federal Acquisition Regulation Supplement (DFARS) violations when identity assurance can’t be demonstrated to Department of Defense auditors
- Contract loss and facility clearance suspension when a security incident triggers investigation, putting existing contracts and future eligibility at risk
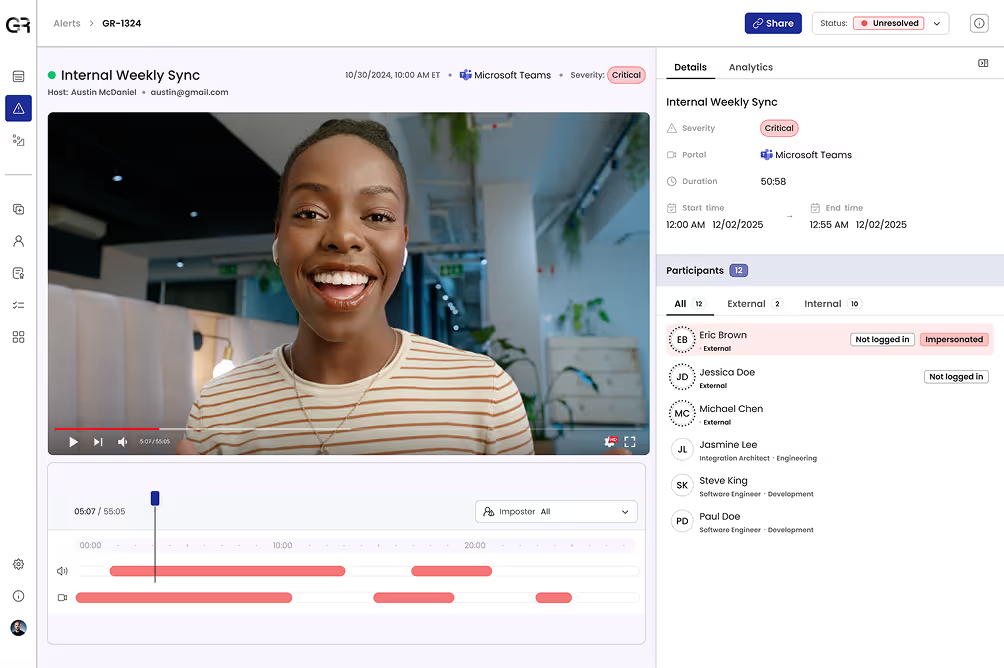
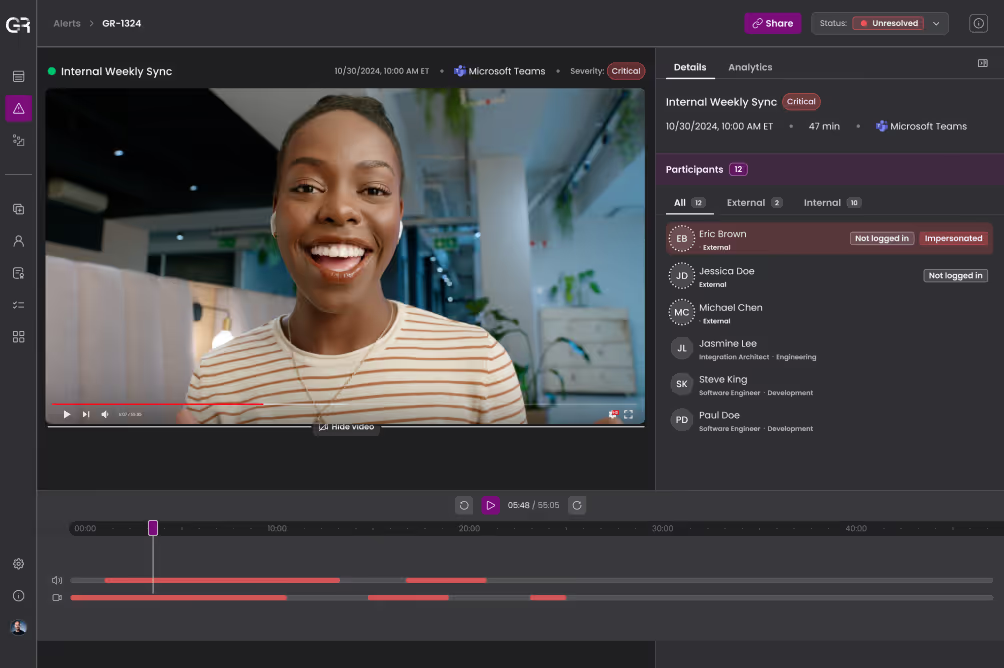
Rigorous Deepfake Detection
GetReal identifies AI-generated voices, face-swapped video participants, and synthetic personas in program briefings, executive meetings, and vendor communications. Detection grounded in digital forensics produces evidence-backed findings that hold up in investigations and regulatory inquiries.
Continuous Identity Verification
Continuously validate the identity of personnel, subcontractors, and supply chain partners across every digital interaction. Identity templates built over time detect when an individual is not whom they claim to be before access is granted or information is shared.
Adaptive, Automated Response
Enforce identity policies in real time across secure communications platforms, automatically flagging or terminating interactions when identity cannot be confirmed. Response actions integrate with existing security stacks to support access control requirements without adding manual burden.
Global Threat Intelligence
Curated threat intelligence on nation-state adversaries’ identity tactics and known personas correlates signals across programs, facilities, and the broader defense community. This turns isolated detections into industry-wide defense.
Why Defense Industrial Leaders Choose GetReal
Defense leaders choose GetReal because the human layer is where nation-state adversaries have found a reliable entry point, and it’s where traditional controls lack reach.
GetReal extends zero-trust identity security to hiring processes, personnel interactions, and vendor communications that existing security solutions cannot see, detecting and ejecting nation-state actors before they gain persistent access.
Continuous identity assurance and forensic-grade audit trails across communications strengthen CMMC and DFARS compliance and give teams evidence that holds up to scrutiny.
Find Your GetReal Use Case
Understand Deepfake & AI-Powered Identity Threats by Role
Find Out Where Your Human Layer is Exposed