Secure Your IT Service Desk Against Social Engineering

IT Help Desk Attacks by the Numbers

Source: SEC Filing
.png)
Source: Verizon DBIR
.png)
Source: Unit 42
Why Attackers Target IT Help Desks for Account Takeover
Scattered Spider didn’t use a software vulnerability, zero-day exploit, or malware to infiltrate MGM Resorts or Caesars Entertainment. They called the IT service desk, impersonated an employee, and convinced agents to reset credentials. That gave them full network access resulting in the deployment of ransomware, a $100 million loss for MGM, and a $15 million ransom paid by Caesars.
Why Knowledge-Based Authentication Fails at the Help Desk
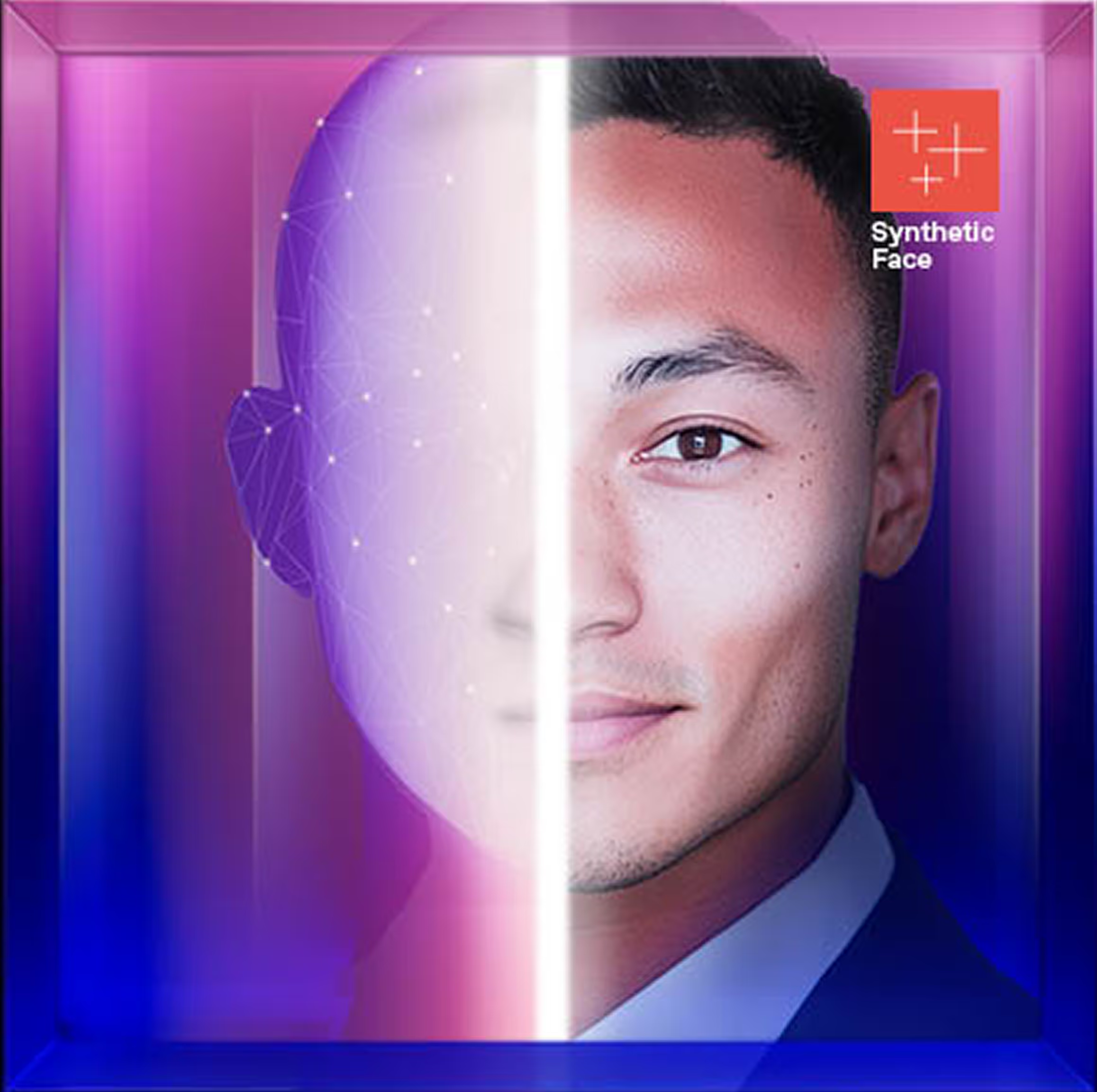
IT service desks sit at the center of identity, access, and human judgement. Traditional security controls stop before the human layer and so cannot know or verify the person or presence on the other end of a digital interaction. Biometric authentication was not built to withstand AI-generated images, audio, and video – leaving IT service desks vulnerable to spoofed voices, faces, and presence in real time. Agents must make high-stakes decisions while attackers use deepfakes, harvested data, and playbooks specifically designed to deceive them.
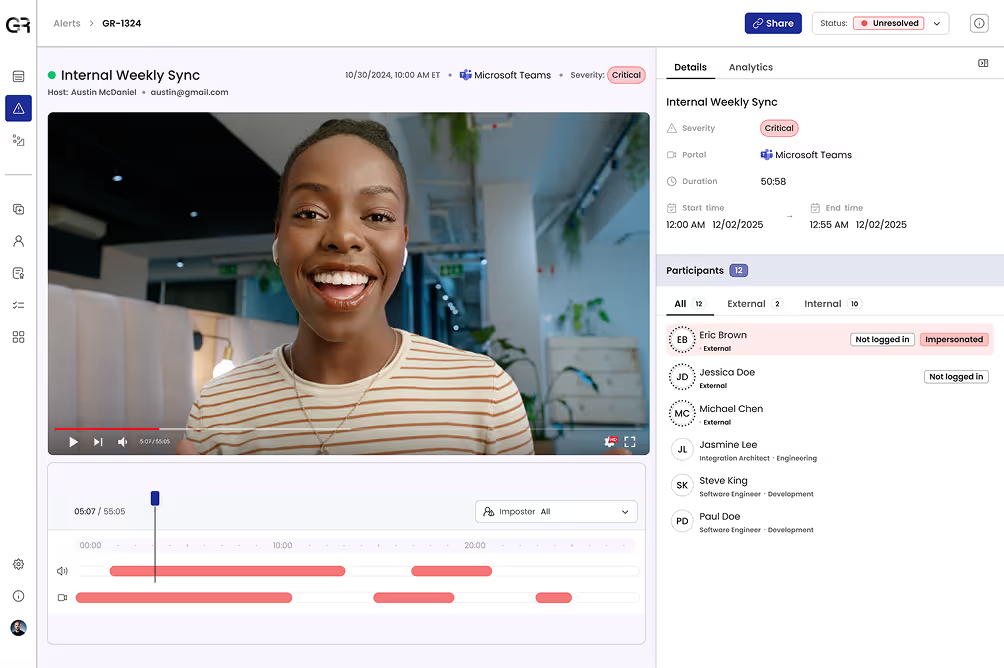
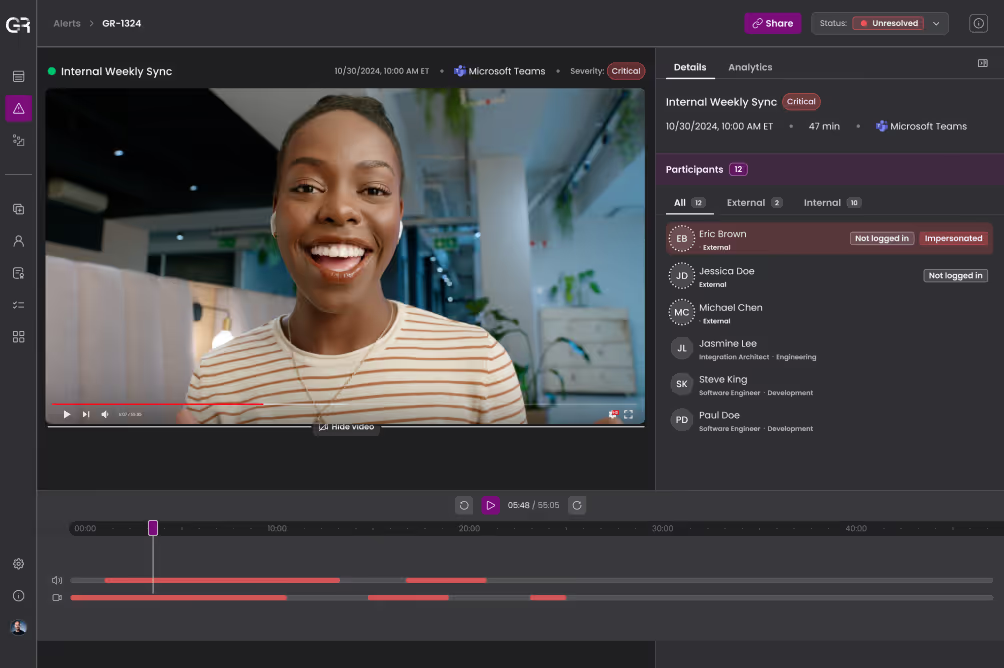
Rigorous Deepfake Detection
Eliminate bad actors that use AI-manipulated audio, video, or images from the queue quickly. With deepfake detection grounded in forensic science, not generic AI classification scores, deceptive content is flagged with high confidence.
Continuous Identity Verification
Confirm that the person on the other end of an interaction is the employee they claim to be. Identity templates created and updated across time and channels protect employees and expose imposters even when they can answer basic knowledge questions.
Adaptive, Automated Response
Ensure consistent response with automated policy enforcement that doesn’t burden IT service desk agents. Calls can be terminated, escalated to specialists, or routed to fraud teams based on trustworthy, forensic evidence of deception.
Global Threat Intelligence
Identify and eject known fraudsters and repeat offenders from service desk interactions with curated intel spanning your environment and the wider threat landscape. Correlates patterns automatically to block adversaries in real time.
Outcomes for IT Service Desks
- Prevent account takeover resulting from IT service desk social engineering including credential reset and MFA re-enrollment
- Ensure consistent scrutiny of IT service desk callers to reduces agents’ cognitive load
- Demonstrate diligent monitoring and control of access and account recovery workflows to leadership and auditors

Understand Deepfake & AI-Powered Identity Threats by Role
See Your IT Service Desk Through an Attacker’s Eyes