Validate Your Workforce for Competitive Advantage

The Stakes in Business Process Outsourcing
Source: Deloitte
.avif)
Source: IBM
Source: MasterCard
How Business Process Outsourcing Firms Are Exposed
Enterprises that outsource a business function ask the same question: how do we know the people on the other side of this relationship are actually who they say they are?
BPO firms have historically answered that question with background checks at hire and security certifications on paper, but AI has broken that model. Nation-state operatives and organized fraud rings infiltrate BPO workforces through AI-fabricated personas, then use that access to exfiltrate client data, redirect payments, or establish persistent footholds across multiple client environments.
A single fraudulent worker inside a BPO firm is a portfolio-wide exposure that puts a firm’s reputation and revenue at risk.
What’s at Risk
- Contract loss and competitive disadvantage when clients choose BPO partners who demonstrate continuous workforce identity assurance over those who only produce background checks
- Portfolio-wide exposure when a single fraudulent employee or impersonator gains access to multiple client environments through shared BPO infrastructure
- BPO firm liability when an incident involving workforce identity failure results in client data breaches, fraud losses, or regulatory violations
- RFP disqualification as enterprise procurement teams add identity assurance requirements to vendor security questionnaires that a SOC 2 certifications alone no longer satisfy
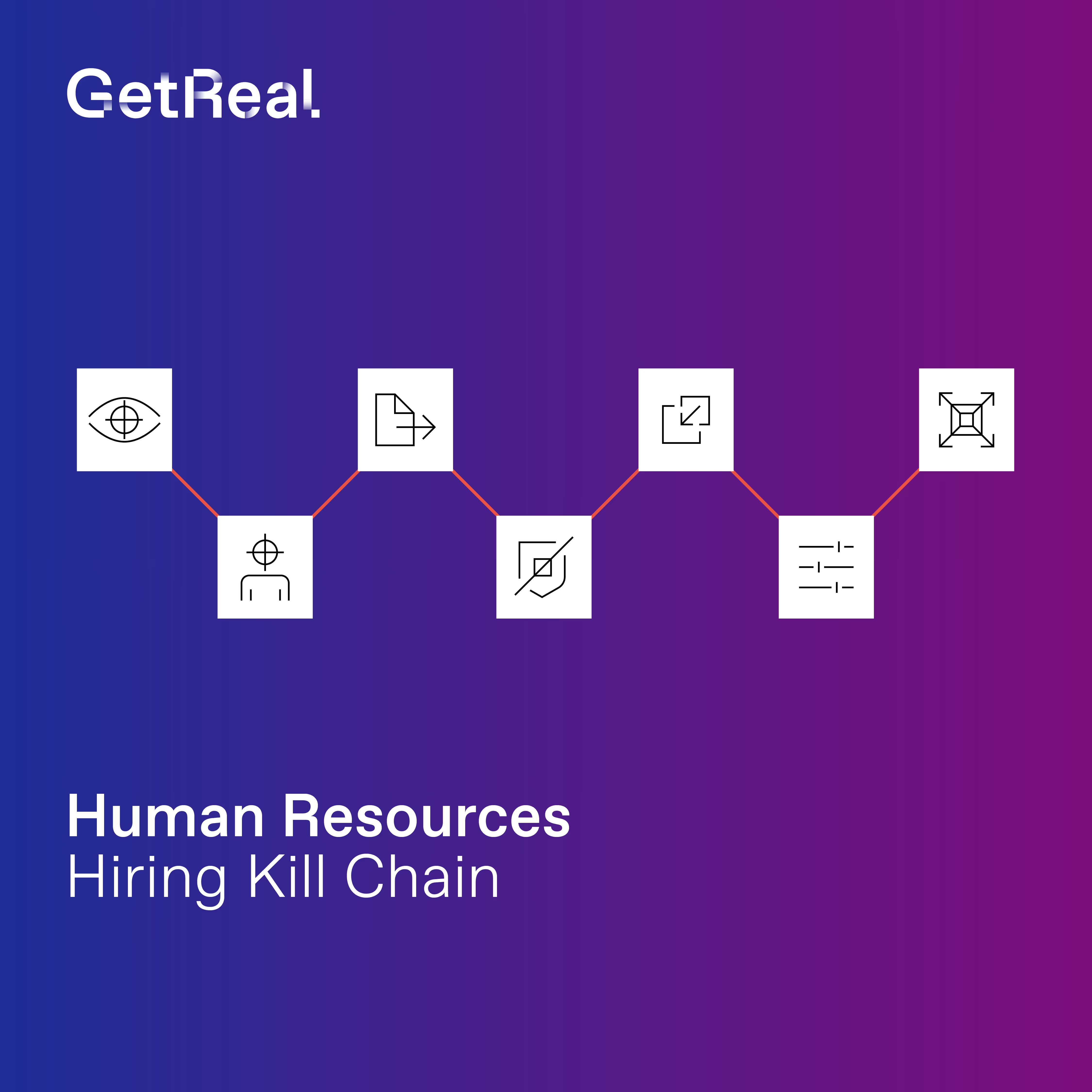
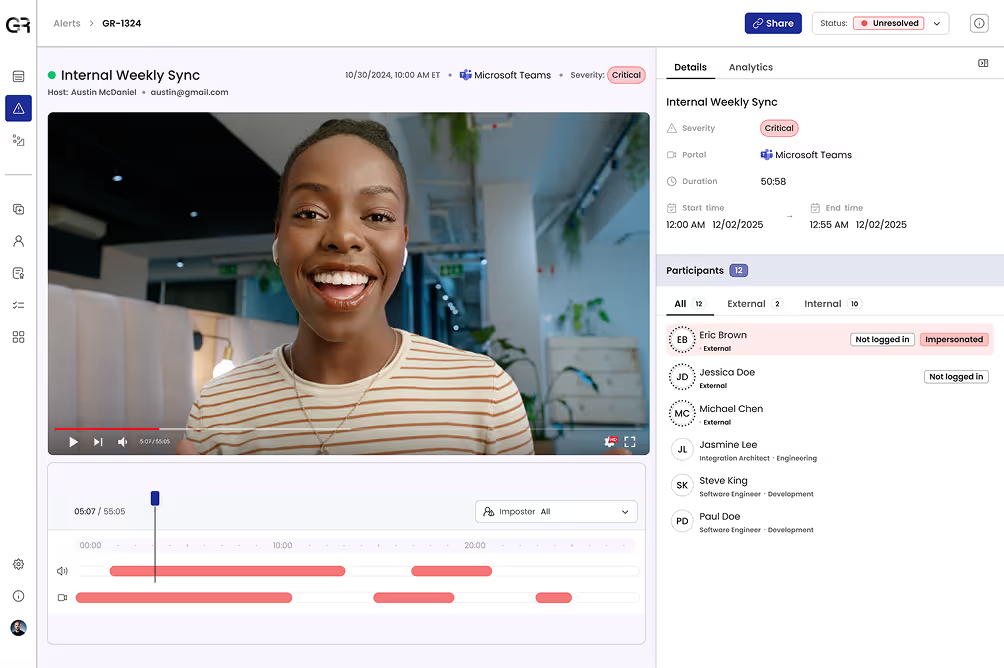
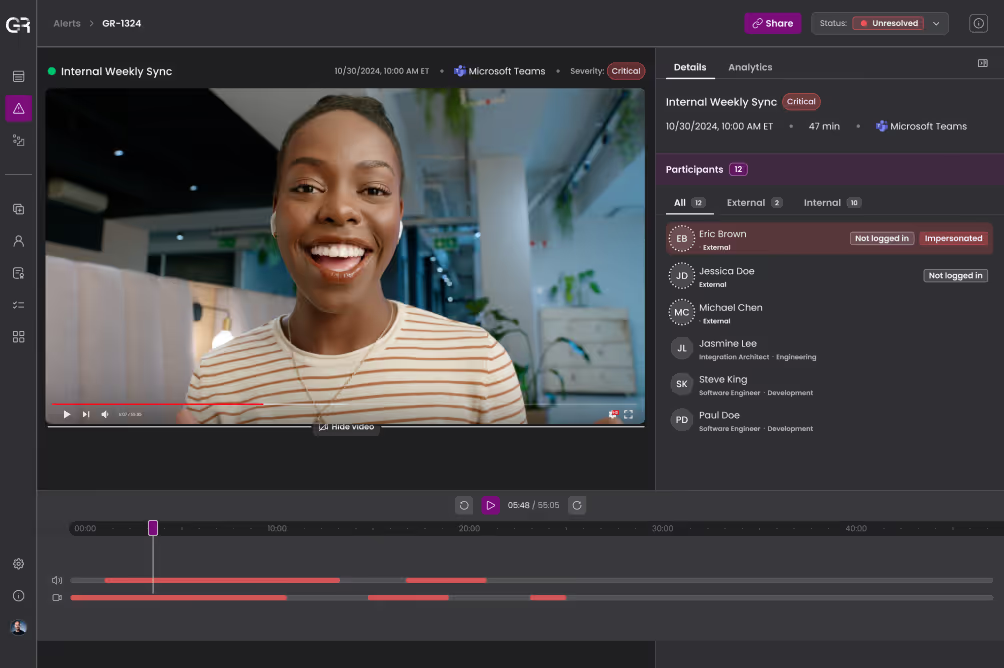
Rigorous Deepfake Detection
Identify AI-generated personas attempting to enter the workforce under cover of manipulated voices or video and fabricated professional profiles in onboarding workflows. Forensic-grade detection produces audit-ready evidence to satisfy client security reviews and regulatory inquiries.
Continuous Identity Verification
Continuously confirm that the people working on client programs are the same people who were originally hired and credentialed. Identity profiles built over time and across calls, video sessions, and internal systems provide a living record of workforce authenticity that background checks alone cannot provide.
Adaptive, Automated Response
Enforce identity policies across every client program automatically, without adding overhead to operations teams or friction for legitimate agents. When anomalies are detected, responses (e.g., escalation, flagging, session termination) trigger based on pre-set rules, giving clients confidence that violations are caught and actioned quickly.
Global Threat Intelligence
Detect known fraudsters, synthetic personas, and nation-state-linked workers attempting to infiltrate your hiring pipelines or re-enter through partner networks. Cross-environment intelligence means a threat identified in one client program protects the entire portfolio.
Why BPO Leaders Choose GetReal Security
BPO leaders choose GetReal because workforce trust can’t simply be claimed, it needs to be proven to clients. GetReal gives BPO firms continuous, verifiable identity assurance that wins enterprise contracts, satisfies the toughest client security audits, and commands premium pricing in competitive RFPs.
When fraudulent employees or impersonators are detected before they move laterally across client environments, a portfolio-wide vulnerability becomes a controlled risk. And when audits come, forensic evidence of ongoing workforce verification replaces point-in-time certifications that sophisticated clients won’t accept at face value.
Find Your GetReal Use Case
Understand Deepfake & AI-Powered Identity Threats by Role
Give Your Next BPO Prospect Another Reason to Choose You